BwUniCluster 2.0 User Access/SSH Keys
|
NOTE: Interactive SSH Keys are not valid all the time, but only for one hour after the last 2-factor login. They have to be "unlocked" by entering the OTP and service password. Please see the more detailed description in the Section Registering an interactive key.
|
SSH Keys are a mechanism for logging into a computer system without having to enter a password. Instead of authenticating yourself with something you know (a password), you prove your identity by showing the server something you have (a cryptographic key).
The usual process is the following:
- The user generates a pair of SSH Keys, a private key and a public key, on their local system. The private key never leaves the local system.
- The user then logs into the remote system using the remote system password and adds the public key to a file called ~/.ssh/authorized_keys .
- All following logins will no longer require the entry of the remote system password because the local system can prove to the remote system that it has a private key matching the public key on file.
While SSH Keys have many advantages, the concept also has a number of issues which make it hard to handle them securely:
- The private key on the local system is supposed to be protected by a strong passphrase. There is no possibility for the server to check if this is the case. Many users do not use a strong passphrase or do not use any passphrase at all. If such a private key is stolen, an attacker can immediately use it to access the remote system.
- There is no concept of validity. Users are not forced to regularly generate new SSH Key pairs and replace the old ones. Often the same key pair is used for many years and the users have no overview of how many systems they have stored their SSH Keys on.
- SSH Keys can be restricted so they can only be used to execute specific commands on the server, or to log in from specified IP addresses. Most users do not do this.
To fix these issues it is no longer possible to self-manage your SSH Keys by adding them to the ~/.ssh/authorized_keys file on bwUniCluster. SSH Keys have to be managed via the central bwIDM system instead. Existing authorized_keys files are ignored.
Minimum requirements for SSH Keys
Algorithms and Key sizes:
- 2048 bits or more for RSA
- 521 bits for ECDSA
- 256 Bits (Default) for ED25519
ECDSA-SK and ED25519-SK keys (for use with U2F Hardware Tokens) cannot be used yet.
Please set a strong passphrase for your private keys.
Adding a new SSH Key
1. Log into https://bwidm.scc.kit.edu.
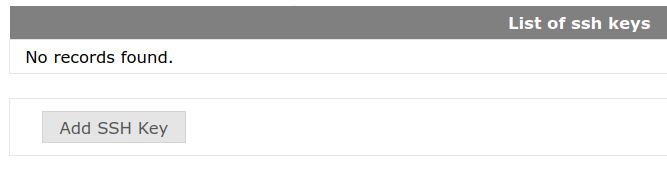
2. Click on My SSH Pubkeys or Meine SSH Pubkeys in the main menu.
3. Click on the Add SSH Key or SSH Key hochladen button.
4. A new window will appear. Enter a name for the key and paste your SSH public key (NOT the private key!) into the box labelled "SSH Key:". Click on the button labelled Add or Hinzufügen. Note that you cannot add an SSH public key that has already been used before.
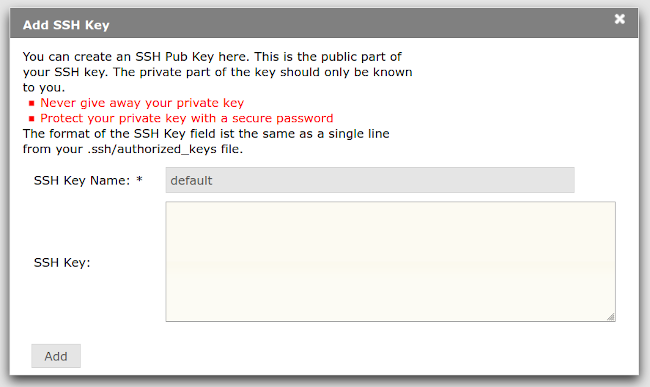
5. If everything worked fine your new key will show up in the user interface:
Newly added keys have a validity of three months. After that they will be revoked and put on a blocklist, so they cannot be used again.
Once you have added SSH Public Keys to the system you can bind them to one or more services for one of two reasons: To use them for generic, interactive logins (Interactive Key) , or for automated logins (Command Key).
Registering an Interactive Key
Interactive Keys can be used to log into a system for normal interactive use. They are not valid all the time, but only for one hour after the last 2-factor login. This means that on the first attempt to log into the bwUniCluster 2.0 system your SSH key will not be accepted, but you have to log in with an One-Time Password (OTP) and your service password. After that you won't have to enter the OTP and service password anymore for one hour because your SSH Key has been unlocked. After the hour has passed, you have to enter the OTP and service password again on your next login, and then your SSH Key will be unlocked for another hour.
Perform the following steps to register an interactive key:
1. Log into https://bwidm.scc.kit.edu.
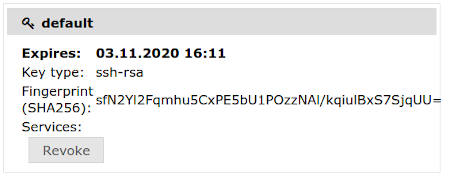
2. Locate the requested service (bwUniCluster) in the main menu and click on Set SSH Key or SSH Key setzen in the main menu.
3. The upper block shows the SSH Keys currently registered for the service. The lower block shows all SSH public keys which have been added to your account. Locate the SSH Key you want to use and click on Add or Hinzufügen.
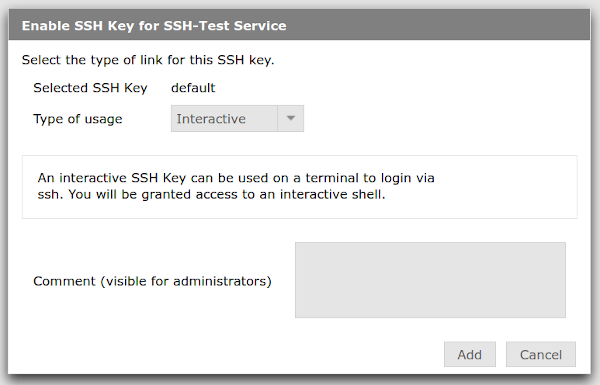
4. A new window appears. Choose Interactive under Type of usage, enter an optional comment and click on Add or Hinzufügen.
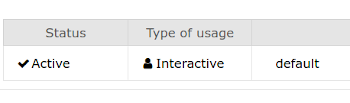
5. Your SSH key has now been registered to the service and can be used.
Registering a Command Key
Passphrases, 2-factor authentication and service passwords make it impossible to integrate many scientific workflows with bwUniCluster 2.0. We therefore offer a second type of registration: Command Keys, special keys which can be used for automation.
Command Keys are always valid and don't have to be unlocked. This makes these keys extremely valuable to a possible attacker and poses a security risk, so we enforce additional restrictions on these keys:
- They have to be restricted to a single command which can be executed.
- They have to be restricted to a single IP address (e.g. the workflow server) or a small number of IP addresses (e.g. the subnet of the institute).
- They have to be checked and approved by an HPC administrator before they can be used.
- The validity is reduced to one month.
The process for registering a Command Key is the same as the one for an Interactive Key, but after selecting Command under Type of usage two additional field labelled Command and From (network address) appear which have to be filled in. Please also provide a comment to speed up the approval process.
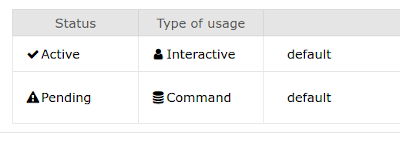
After the key has been added, it will be marked as Pending:
[[File:Bwunicluster 2.0 access ssh keys service add command.png|center]
You will receive an e-mail as soon as the key has been approved and can be used.
Revoke/Delete an SSH Key
1. Log into https://bwidm.scc.kit.edu.
2. Click on My SSH Pubkeys or Meine SSH Pubkeys in the main menu.
3. Click on the Revoke or Zurückziehen button next to the SSH Key you want to revoke.
Please note that revoked keys are blocked and cannot be used again.