Registration/2FA: Difference between revisions
m (→How 2FA works) |
|||
| Line 28: | Line 28: | ||
* LastPass Authenticator for [https://play.google.com/store/apps/details?id=com.lastpass.authenticator Android], [https://apps.apple.com/us/app/lastpass-authenticator/id1079110004 iOS] or [https://lastpass.com/auth/ Windows] |
* LastPass Authenticator for [https://play.google.com/store/apps/details?id=com.lastpass.authenticator Android], [https://apps.apple.com/us/app/lastpass-authenticator/id1079110004 iOS] or [https://lastpass.com/auth/ Windows] |
||
* Aegis Authenticator for [https://play.google.com/store/apps/details?id=com.beemdevelopment.aegis Android (Google Play)] or [https://f-droid.org/en/packages/com.beemdevelopment.aegis/ Android (F-Droid)] ([https://getaegis.app/ Web Page]) |
* Aegis Authenticator for [https://play.google.com/store/apps/details?id=com.beemdevelopment.aegis Android (Google Play)] or [https://f-droid.org/en/packages/com.beemdevelopment.aegis/ Android (F-Droid)] ([https://getaegis.app/ Web Page]) |
||
* andOTP Authenticator for [https://play.google.com/store/apps/details?id=org.shadowice.flocke.andotp Android (Google Play] or [https://f-droid.org/packages/org.shadowice.flocke.andotp/ Android (F-Droid)] ([https://github.com/andOTP/andOTP GitHub]) |
* andOTP Authenticator for [https://play.google.com/store/apps/details?id=org.shadowice.flocke.andotp Android (Google Play)] or [https://f-droid.org/packages/org.shadowice.flocke.andotp/ Android (F-Droid)] ([https://github.com/andOTP/andOTP GitHub]) |
||
* OTP Auth for [https://apps.apple.com/app/otp-auth/id659877384 iOS] |
* OTP Auth for [https://apps.apple.com/app/otp-auth/id659877384 iOS] |
||
* (Authy for [https://play.google.com/store/apps/details?id=com.authy.authy Android], [https://apps.apple.com/us/app/authy/id494168017 iOS], [https://authy.com/download/ Mac, Windows or Linux]) requires account |
* (Authy for [https://play.google.com/store/apps/details?id=com.authy.authy Android], [https://apps.apple.com/us/app/authy/id494168017 iOS], [https://authy.com/download/ Mac, Windows or Linux]) requires account |
||
Revision as of 12:57, 11 February 2022
Generate a Second Factor (2FA)
To improve security a 2-factor authentication mechanism (2FA) is being enforced for logins to bwUniCluster/bwForClusters. In addition to the service password a second value, the second factor, has to be entered on every login.
How 2FA works
|
It is very important that the device that generates the One-Time Passwords and the device which is used to log into the bwUniCluster/bwForClusters are not the same. Otherwise an attacker who gains access to your system can steal both the service password and the secret key of the Software Token application, which allows them to generate One-Time Passwords and log into the HPC system without your knowledge. |
On the bwUniCluster/bwForClusters we use six-digit, auto-generated, time-dependent one-time passwords (TOTP). These passwords are generated by a piece of software which is part of a special hardware device (a hardware token) or of a normal application running on a common device (a software token).
The Token has to be synchronized with a central server before it can be used for authentication and then generates an endless stream of six-digit values (TOTPs) which can only be used once and are only valid during a very short interval of time. This makes it much harder for potential attackers to access the HPC system, even if they know the regular service password.
Typically a new TOTP value is generated every 30 seconds. When the current TOTP value has once been used successfully for a login, it is depleted and one has to wait up to 30 seconds for the next TOTP value.
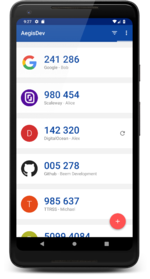
The most common solution is to use a mobile device (e.g. your smartphone or tablet) as a Software Token by installing one of the following apps:
- Google Authenticator for Android or iOS
- Microsoft Authenticator for Android or iOS (Web Page)
- LastPass Authenticator for Android, iOS or Windows
- Aegis Authenticator for Android (Google Play) or Android (F-Droid) (Web Page)
- andOTP Authenticator for Android (Google Play) or Android (F-Droid) (GitHub)
- OTP Auth for iOS
- (Authy for Android, iOS, Mac, Windows or Linux) requires account
- (On Linux you can use KeepassXC or otpclient)
These are only suggestions. You can use any application compatible with the TOTP standard.
If you don't want to use a smartphone, we recommend using a hardware token, such as Yubikey or another TOTP-compatible device. Yubico OTP is also supported if you want to use your Yubikey without depending on having a six-digit code displayed. But you can also use the Yubikey as a generator for six-digit TOTP.
Token Management
|
bwUniCluster/bwForCluster Tokens are generally managed via the Index -> My Tokens menu entry on the registration pages for the clusters. Here you can register, activate, deactivate and delete tokens.
To activate the second factor, please perform the following steps:
1. Select the registration server of the cluster for which you want to create a second factor and login to it:
→ Registration server for bwUniCluster 2.0 and bwForCluster JUSTUS 2 (2FA tokens are valid for both clusters; KIT members can reuse their existing hardware and software tokens)
→ Registration server for bwForCluster MLS&WISO
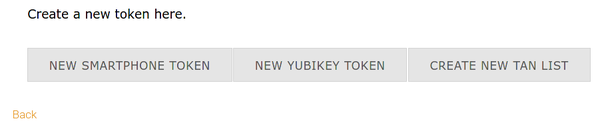
2. Create a new "Smartphone" or "Yubikey Token".
3. Create a new "TAN List" (backup TAN list).
4. Repeat step 2. for additional tokens.
Registering a new Software Token using a Mobile APP
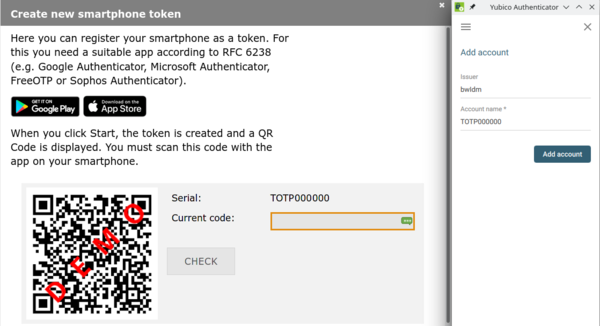
1. Registering a new Token starts with a click NEW SMARTPHONE TOKEN.
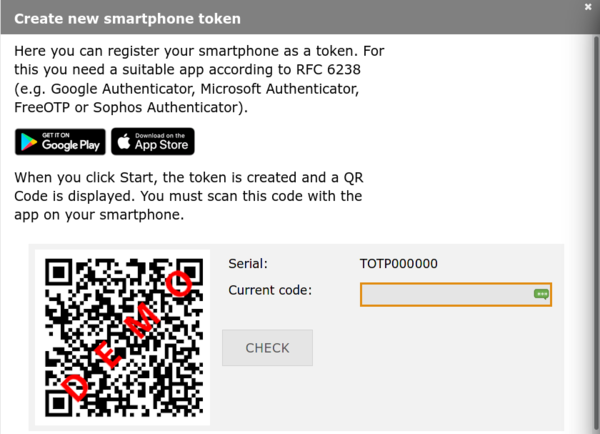
2. A new window opens. Click Start to generate a new QR code. This may take a while.
|
The QR code contains a key which has to remain secret. Only use the QR code to link your software token app with bwIDM/bwServices in the next step. Do not save the QR code, print it out or share it with someone else. |
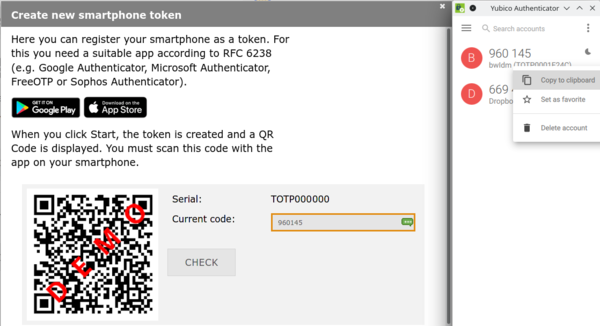
3. Start the software token app on your separate device and scan the QR code. The exact process is a little bit different in every app, but is usually started by pressing on a button with a plus (+) sign or an icon of a QR code.
4. Once the QR code has been loaded into your Software Token app there should be a new entry called bwIDM or bwServices (MLS&WISO). Generate an One-Time-Password by pressing on this entry or selecting the appropriate button/menu item. You will receive a six-digit code. Enter this code into the field labeled "Current code:" in your bwIDM browser window to prove that the connection has worked and then click Check.
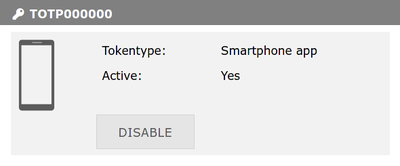
5. If everything worked as expected, you will be returned to the My Tokens screen and there will be a new entry for your software token.
6. Repeat the process to register additional tokens. Please register at least the "Backup TAN list" in addition to the hardware/software token you plan to use regularly.
Registering a Yubikey OATH TOTP
Yubikey OATH TOTP generates the TANs on your Yubikey and therefore you can use different computers and Android phones to generate these codes. Please download and install Yubico Authenticator for Desktop (or Android) first. Insert your Yubikey in your computer. "Yubikey OTP" (not "Yubikey OATH TOTP") is even easier and you don't need a device that displays the six-digit code or extra software (go to step Yubikey OTP).
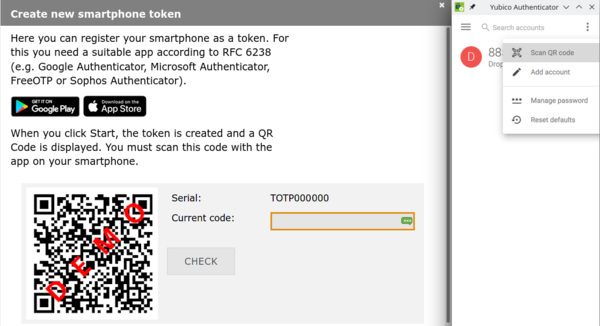
1. Registering a new Token starts with a click NEW SMARTPHONE TOKEN.
2. A new window opens. Click Start to generate a new QR code. This may take a while.
|
The QR code contains a key which has to remain secret. Only use the QR code to link your software token app with bwIDM/bwServices in the next step. Do not save the QR code, print it out or share it with someone else. |
3. Start the Yubico Authenticator on your OS, click the three vertical dots in the upper right corner and select Scan QR code.
4. Yubico Authenticator automatically translates the QR code to a new entry called bwIDM or bwServices (MLS&WISO). Click Add account.
5. You will receive a six-digit code. Enter this code into the field labeled "Current code:" in your bwIDM browser window to prove that the connection has worked and then click CHECK.
6. If everything worked as expected, you will be returned to the My Tokens screen and there will be a new entry for your software token.
7. Repeat the process to register additional tokens. Please register at least the "Backup TAN list" in addition to the hardware/software token you plan to use regularly.
Yubikey OTP
Yubikey OTP is even easier and you don't need a device that displays the six-digit code or extra software. New Yubikeys are already configured to provide Yubikey OTP in slot 1. If you need to configure your Yubikey, read this documentation.
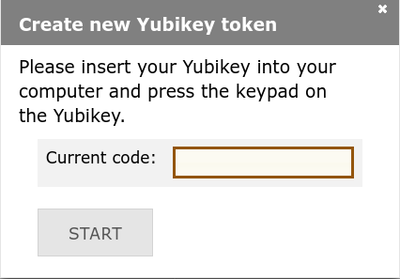
1. If you want to use Yubico OTP, you can click NEW YUBIKEY TOKEN instead.
2. Yubikey OTP is configured to slot 1 on new Yubikeys, so you only need to click in the text box and then touch the metal part of your Yubikey. Please refer to this documentation on how to configure your Yubikey.
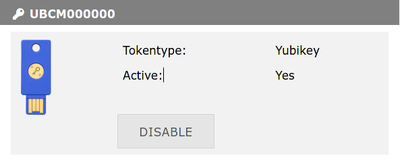
3. If everything worked as expected, you will be returned to the My Tokens screen and there will be a new entry for your Yubikey.
4. Repeat the process to register additional tokens. Please register at least the "Backup TAN list" in addition to the hardware/software token you plan to use regularly.
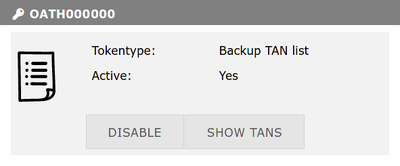
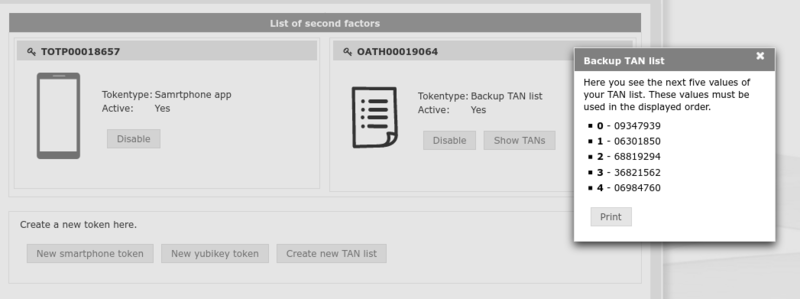
Backup TAN List
|
Passwords from the "Backup TAN list" should only be used if no other token is left. Please do not use the Backup TANs for regular cluster login, because you have only a limited number of TANs. Each TAN can only be used once. |
1. Please create at least one "Backup TAN list" by clicking CREATE NEW TAN LIST.
2. Click START. You will be redirected to the My Tokens screen and there will be a new entry for your backup TANs.
3. Click SHOW TANS, print the codes and keep then in a separate place for emergencies.
4. Repeat the process to register additional tokens.
Deactivating a Token
Click Disable next to the Token entry on the My Tokens screen.
Deleting a Token
After a Token has been disabled a new button labeled Delete will appear. Click on it to delete the token.
Lost Token
If you have lost a token, please create a new one. If you change your phone, please migrate your tokens first or register your new mobile app under "My Tokens". If you no longer have valid tokens (mobile app, hardware token, Yubikey or backup TAN), you will need to contact the ticket system. Please note that this process may take some time and also means additional work for the operators.